Note to Readers: Welcome to ethicbreach.com, where we dive deep into the wild world of hacking—for good. This article is all about understanding crypto wallet vulnerabilities to sharpen your ethical hacking skills. The info here is for educational purposes only—don’t use it to harm, steal, or break laws. Always get permission before testing, and let’s use this knowledge to lock down systems, not loot them. Stay legit, stay sharp, and enjoy the game!
The Crypto Gold Rush: Why Wallets Are Prime Targets
Picture this: a digital vault stuffed with Bitcoin, Ethereum, or some shiny altcoin, just sitting there on the blockchain, waiting. Cryptocurrency wallets are the new bank vaults, and black hat hackers are the modern-day bandits itching to crack them open. Why? Because crypto’s decentralized, pseudonymous nature makes it a thief’s paradise—once it’s gone, it’s damn near untraceable. In 2024 alone, over $2 billion in crypto got snatched, according to Chainalysis. For ethical hackers, this is our playground to figure out how the bad guys do it—and how to stop them.
In this post, we’re pulling off a virtual heist. We’ll break down how crypto wallets work, where they bleed vulnerabilities, and how you can exploit them (ethically, of course). From hot wallets to cold storage, we’ll dissect the tech and show you the cracks. Buckle up—this is gonna get technical, dark, and fun.
Wallet 101: The Tech Behind the Treasure
First, let’s rip apart the basics. A crypto wallet isn’t a physical thing—it’s software or hardware that holds two keys: a public key (your address, like a bank account number) and a private key (your secret code to spend the loot). Lose the private key? You’re screwed. Steal it? Jackpot.
Wallets come in two flavors:
- Hot Wallets: Online, connected, and convenient—think mobile apps (MetaMask, Trust Wallet) or browser extensions. They’re fast but exposed.
- Cold Wallets: Offline, like hardware devices (Ledger, Trezor) or paper backups. Secure, but not invincible.
The blockchain itself is a fortress—cracking it is near impossible with current tech. But wallets? They’re the weak link, built on software, humans, and sloppy habits. That’s where we strike.
Cracking Hot Wallets: The Low-Hanging Fruit
Hot wallets are the juiciest targets—always online, always vulnerable. Here’s how a black hat might raid one, and how you can test the defenses ethically.
Phishing the Private Key
Step one: trick the mark. Phishing’s old-school but gold. Craft a fake MetaMask login page—HTML, CSS, a sprinkle of JavaScript—and host it on a sketchy domain. Send it via email: “Your wallet’s compromised, log in to secure it!” The second they enter their seed phrase (that 12-24 word recovery key), you’ve got their private key. Game over.
Tech Bit: Seed phrases are hashed with BIP-39 standards into a 256-bit private key. Snag that phrase, and you can regenerate the key on your own device using a tool like Electrum or a Python script with the pycoin library:
from pycoin.key import Key
seed = "abandon ability ... " # 12-word example
key = Key.from_text(seed)
print(key.secret_exponent()) # Your private key
Ethical Hack: Test your own dummy wallet. Set up a phishing page (localhost only, never live), see how convincing it is, then shred it. Teach users to spot fakes—check URLs, use 2FA, and never paste seed phrases.
Clipboard Hijacking
Here’s a sneaky one: malware that watches your clipboard. Users copy their wallet address to send crypto, but the malware swaps it with the attacker’s address. One paste later, funds vanish. Black hats deploy this via trojans or browser extensions gone rogue.
Tech Bit: A simple JavaScript snippet can do it:
document.addEventListener('copy', function(e) {
e.clipboardData.setData('text/plain', 'bc1qeviladdresshere');
e.preventDefault();
});
Ethical Hack: Write a proof-of-concept (PoC) script, test it on your own machine, and demo how antivirus or browser security catches it—or doesn’t. Push users to verify addresses manually.
Cold Wallet Takedown: Cracking the Ice
Cold wallets sound safe—offline, untouchable. Wrong. Physical access or human error can turn them into loot bags. Let’s break in.
Seed Phrase Extraction
Most cold wallet users scribble their seed phrase on paper or store it digitally (big mistake). A black hat with physical access—say, a shady roommate—snaps a pic, and they’re in. Hardware wallets like Ledger use a PIN, but if you’ve got the seed, PINs don’t matter.
Tech Bit: Seed phrases follow BIP-32/BIP-39 derivation paths (e.g., m/44'/0'/0'/0/0). Plug it into a tool like ian coleman’s BIP39 generator, and you’ve got the keys to the kingdom.
Ethical Hack: Simulate this with a test wallet. Hide a dummy seed phrase, “steal” it, and recover the wallet. Show why metal backups or split storage (Shamir’s Secret Sharing) beat paper.
Supply Chain Attacks
Ever bought a “new” Ledger off eBay? Black hats tamper with hardware wallets pre-sale, preloading malware or fake firmware. Plug it in, and it silently leaks your keys. In 2023, a batch of compromised Trezors hit the dark web—buyers lost millions.
Tech Bit: Firmware’s signed, but a custom bootloader can bypass checks. Tools like STM32CubeProgrammer can flash rogue code if you’ve got the device’s guts open.
Ethical Hack: Inspect a legit device’s firmware hash (e.g., Ledger’s SHA-256 checksum) against the official release. Teach users to buy direct from manufacturers.
Exchange Wallets: The Big Score
Crypto exchanges (Coinbase, Binance) hold hot wallets with billions. Black hats dream of these heists—think Mt. Gox 2014 or KuCoin 2020. Here’s how they hit them.
API Key Theft
Users with trading bots often store API keys—access codes for their exchange accounts—on their PC. Malware like RedLine Stealer sniffs these out, giving attackers full control to drain funds.
Tech Bit: An API key with withdrawal permissions is a golden ticket. Pair it with a script:
import ccxt
exchange = ccxt.binance({'apiKey': 'stolen_key', 'secret': 'stolen_secret'})
exchange.withdraw('BTC', 1.0, 'bc1qattackeraddress')
Ethical Hack: Set up a test account, generate an API key, and “steal” it with a dummy malware PoC. Show why read-only keys and IP whitelisting save the day.
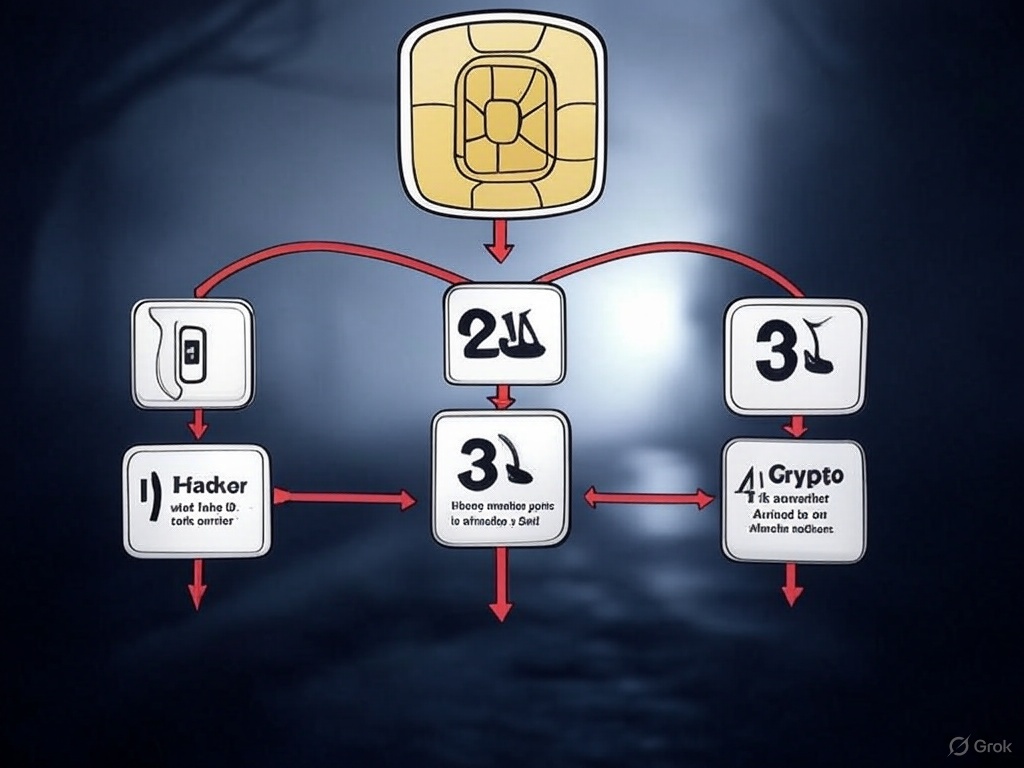
Sim Swapping
Old but brutal: convince a carrier to port the victim’s phone number to your SIM. Reset their exchange 2FA, log in, and clean them out. In 2022, a single swapper nabbed $20M in crypto.
Tech Bit: Social engineering’s key—fake IDs, sob stories to customer service. No code needed, just guts.
Ethical Hack: Call your own carrier, test their verification process (with consent), and report gaps. Push for hardware 2FA like YubiKey over SMS.
Countermeasures: Locking the Vault
Now flip the script—how do you stop this madness? Ethical hackers don’t just break; we build. Here’s the defense playbook:
- Hot Wallets: Use 2FA (not SMS), check URLs religiously, and run wallets in sandboxed environments (e.g., Qubes OS).
- Cold Wallets: Engrave seeds on steel, split them with Shamir’s scheme, and verify hardware authenticity.
- Exchanges: Limit API permissions, use hardware authenticators, and monitor account activity with tools like BlockSec.
Tech Bit: Test your setup with a tool like TruffleHog to sniff out exposed keys in your code or backups:
trufflehog filesystem /path/to/wallet --regex --entropy=True
The Heist Game: Your Move
Crypto heists are a cat-and-mouse game—black hats evolve, and we evolve faster. This isn’t about stealing; it’s about mastering the cracks so you can seal them. Set up a test wallet, run these attacks in a safe sandbox, and see how far you can push. Then lock it down tighter than Fort Knox.
Got a heist story or a defense trick? Drop it in the comments. This is ethicbreach.com—where we play hard, learn deep, and keep the digital world from burning. #ethicbreach